For most internet users, CAPTCHAs are a minor inconvenience; a quick box to tick, a blurry word to decipher, or a grid of traffic lights to identify.
Designed as a frontline defence against bots, CAPTCHAs have become a near-universal feature of the modern web. But as recent findings show, these familiar tools are no longer just about security.
Increasingly, they are being exploited in ways that blur the line between user verification and financial risk.
CAPTCHA stands for “Completely Automated Public Turing test to tell Computers and Humans Apart.”
At their core, these systems are meant to distinguish real users from automated scripts that attempt to spam forms, scrape data, or carry out malicious activity.
Early versions relied on distorted text recognition, but as artificial intelligence improved, CAPTCHAs evolved.
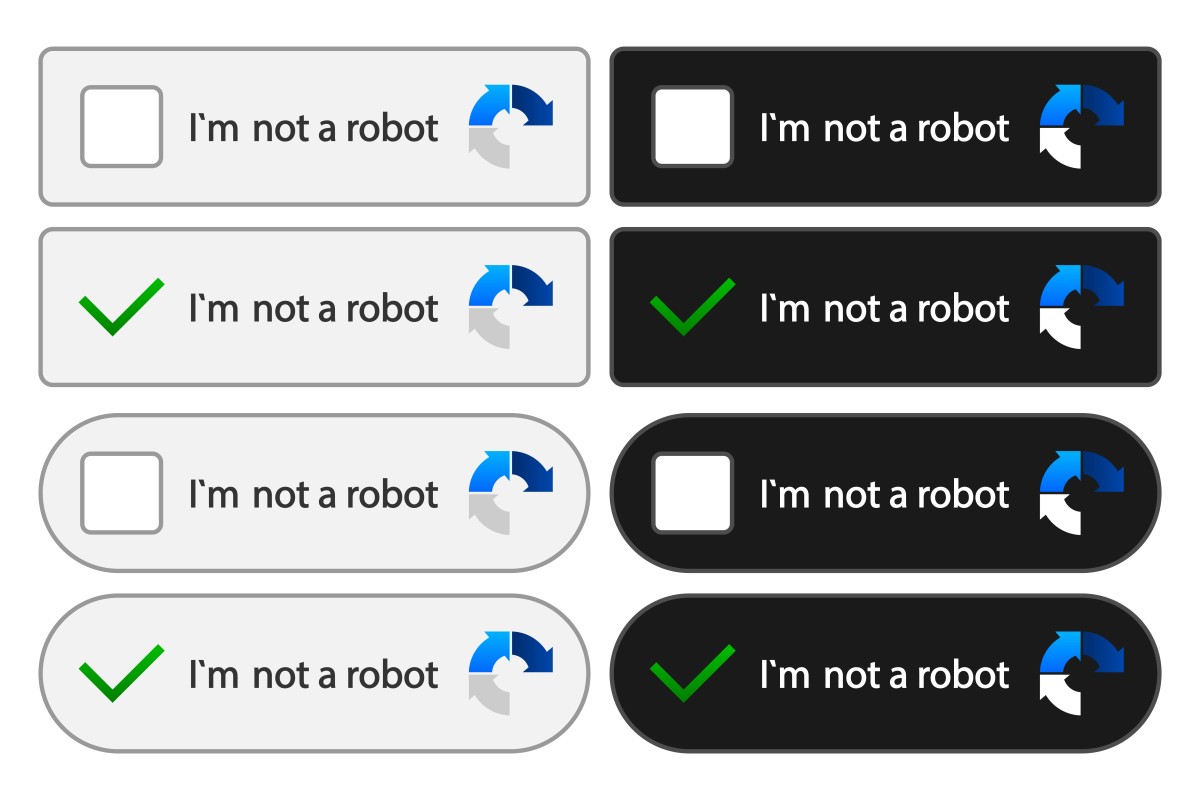
Today’s versions often involve image selection, behavioural tracking, or invisible background checks that assess how a user interacts with a webpage.
This evolution has largely been driven by necessity. Bots have become more sophisticated, capable of solving traditional CAPTCHAs with surprising accuracy.
In response, developers have introduced more complex and user-friendly alternatives, such as “I’m not a robot” checkboxes and passive verification systems that operate without direct user input.
The aim has been to reduce friction while maintaining security; a balance that is increasingly difficult to achieve.
A new scam to be aware of
However, this growing complexity has also created new opportunities for abuse. The latest research highlights how fake CAPTCHA pages are being used to trick users into actions they do not fully understand.
Instead of simply verifying identity, these fraudulent prompts can trigger hidden processes, such as sending premium or international text messages from a user’s phone. Each action may carry only a small charge, but at scale, the financial impact can be significant.
According to Infoblox Threat Intel, fake CAPTCHA pages are being used to trick users into sending large volumes of international text messages, feeding into a long-running fraud model known as international revenue share fraud (IRSF).
The result is unexpected costs for consumers and growing, often unseen, revenue losses for telecom providers.
The research shows that ordinary online interactions can be turned into billable mobile activity without users fully understanding what they are agreeing to.
While each charge may appear small, the cumulative effect can be significant, creating ongoing losses for carriers and a rise in customer complaints and billing disputes.
While IRSF itself is not new, the use of fake CAPTCHAs in this way is considered a newly identified tactic. In these cases, users follow what appears to be a standard verification step, but instead unknowingly trigger the sending of international SMS messages.
Those messages generate charges on the user’s phone bill, with a portion of the revenue flowing back to the operators behind the scam, who control the receiving numbers and the fraudulent CAPTCHA sites.
How does this scam work?
What makes this tactic particularly effective is familiarity. Users are conditioned to trust CAPTCHAs as routine and low-risk.
When presented with a familiar interface, most people will follow instructions without hesitation, assuming the action is necessary to access content.
Cybercriminals are leveraging this trust, embedding malicious functions within what appears to be a standard verification step.
“We’ve been tracking malicious use of traffic distribution systems for a while now, but tying them directly to a long-running SMS fraud scheme is new,” said Dr. Renée Burton, VP of Infoblox Threat Intel. Infoblox Threat Intel is the leading creator of original DNS threat intelligence.
“What makes this operation so effective is not just the fake CAPTCHA itself, but the commercial ad and traffic systems wrapped around it,” she says.
“Affiliate-style infrastructure is being repurposed to industrialize phone fraud, while making it very hard for outsiders to see the full picture.”
The implications extend beyond users. For telecommunications providers, these schemes contribute to a form of fraud known as international revenue share fraud (IRSF), where attackers profit from artificially generated traffic.
While some costs are passed on to customers, carriers often absorb a portion of the losses, along with the reputational damage that comes from billing disputes and customer frustration.
The broader issue is one of transparency. As digital systems become more interconnected, simple actions, like clicking a checkbox, can trigger complex chains of events behind the scenes. Without clear visibility into what those actions entail, users are left vulnerable to manipulation.
CAPTCHAs are unlikely to disappear anytime soon. They remain a critical tool in managing online security and preventing abuse. But their role is changing, and so too is the level of caution required when interacting with them.
What was once a straightforward test of humanity is now part of a much larger and more complicated digital ecosystem, one where trust, convenience and security do not always align as neatly as they once did.